Denial of Service: Difference between revisions
imported>Unknown user No edit summary |
imported>CrackRabbit |
||
| (31 intermediate revisions by 16 users not shown) | |||
| Line 1: | Line 1: | ||
{{FactAlert|This is serious shit and has been known to cause drama and IRL [[Banhammer|Ban Hammers]]. Actually doing this might get you [[Partyvan|v&]]. The information on this page is provided for educational purposes only.}} | |||
<br> | |||
{{FactCat|A Denial of Service attack is any form of attack that prevents legitimate traffic from reaching or being generated by a computer system (most often a webserver). There are many different types of DoS attack but can be grouped into resource consumption denial of service attacks and bandwidth consumption denial of service attacks. Which ever method is employed the result is the same – legitimate traffic to the server system of serving daemon is denied.}} | |||
[[Image:ddos.jpg|thumb|right|Visual approximation.]] | |||
An attempt to take a website or user off the internets by way of [[brute force]] alone (i.e [[CS3|no computer science III]]). It more often than not is simply flooding the target system with ping requests, but it is also possible to use other types of packets destined for any service on the target system that is accepting connections. To make it even better, the iconic DoS attack comes in several /b/tastic flavours. | |||
In order to understand how Denial-of-Service attacks are carried out, it is necessary to understand a bit about how connections are created over the internet. | |||
Please note that people ddosing other players on [[minecraft|Minecraft]] doesn't mean shit. A real ddos attack means taking down a companies website and costing them thousands of dollars in damage. | |||
==The TCP Handshake== | |||
First off, you need some technical information. Remember IP addresses? They have a use other than getting your ass backraided for posting a [[personal army]] request. An IP address (usually) identifies your computer as the recipient of data. In the case of browsing the internet, the web sites you ask to see are sent to your IP address by the web server. | |||
The server has to know your IP address in order to send you anything, though, and your computer needs to know, after you tell it to go to a web page, whether or not the server responded. | |||
On the internet, this is done with a process called the "TCP Handshake." This involves several "packets" of data being exchanged between your computer and the server, illustrated below. | |||
[[File:Tcphandshakebe8.gif]] | |||
SYN-> SYN/ACK -> ACK -> FIN/RST | |||
Afterward, there is a connection open, for the time dictated usually by the systems default TTL (Time to Live) value, over which data can be transferred. | |||
===Exploiting the TCP Handshake=== | |||
With the internet spanning many continents, with hundreds of different ways to get from one place to another, some packets get lost for all sorts of reasons (they expire, get mis-routed or a network link is down). '''If a packet in the TCP handshake gets lost, the connection would fail.''' Packets get lost quite often, but most of the time, your attempts to view web pages succeed. | |||
Why? Because computers send multiple packets to greatly increase the chance that one will get through at each of the three steps, completing the handshake and getting you connected. Similarly, web servers will send multiple "SYN/ACK" packets when the receive a "SYN" packet. If the computer that started the handshake doesn't respond, the following occurs. | |||
[[File:Tcphandshakebrokehs5.gif]] | |||
Most important to remember when exploting the handshake and connection protocol is that servers and any system (routers included) have a maximum number of connection they can track and maintain at once. When the server receives a SYN packet from you, you now take up one allocation of system resources and it will confirm by sending SYN/ACK packets back to you – system resources that aren’t infinite. | |||
==What successful (D)DoS looks like== | |||
* pLsS has quit (Ping timeout: 240 seconds) | |||
* Xero has quit (Ping timeout: 240 seconds) | |||
* Ryan has quit (Ping timeout: 240 seconds) | |||
* TKN has quit (Ping timeout: 240 seconds) | |||
* DocEvil has quit (*.net *.split) | |||
* venuism has quit (*.net *.split) | |||
* nachash has quit (*.net *.split) | |||
* Explodingpiglets has quit (*.net *.split) | |||
* chronos has quit (*.net *.split) | |||
* mooncup has quit (*.net *.split) | |||
* NekoArc has quit (*.net *.split) | |||
==Different Types of Denial of Service Attacks== | |||
===Newtork Bandwidth Consumption=== | |||
First off, the target of an attack is almost always a web server. In order to understand the differences between these two attacks, you must understand, at least on a very basic level, how a web server works. | |||
====How Web Servers Work==== | |||
This is a diagram of a standard web host | |||
[[File:Web Server1.png]] | |||
Notice that people on the internet are asking to see certain websites hosted on the server (Sites 1, 2, and 3; this is a shared hosting plan). The server gets the request, the server looks at the request, finds the requested data, and sends it back out. | |||
All web servers have some physical limit of data that they can process per second, due to a combination of bandwidth limits (i.e. pipe size) and available hardware to utilize the bandwidth and access local data/process commands. We'll say our server can process 5 Gigabits of data each second (or has a 5 gigabit/second bandwidth limit) - if more data than that is being requested, the server will appear to slow down or stop, because it does not have the ability to send data any faster. | |||
Web hosts/servers do not want to operate at their limit - that means that any additional load on the server, any extra visitors, or, say, being linked to from a popular site, will result in their server slowing down. So, they impose bandwidth limits on the sites hosted. The reasoning here is that if a site is taking up HUGE amounts of bandwidth, its data is "clogging" the available connection, and slowing down the other sites. | |||
Now, let's say Site 1 is linked from a popular blog. Suddenly, Requests for Site 1 increase in number, and the server spends more time processing requests to see Site 1 than the other sites. | |||
[[File:Web Server2.png]] | |||
No problem, yet. Now, however, Site 1 is linked to from Slashdot. Requests to see it surge in number. | |||
[[File:Web Server3.png]] | |||
Keep in mind that most web hosts have many, many more than three sites on them - at this point, the server is nearing its physical limit. Usually, one of two things will happen next: | |||
* Site 1 exceeds its bandwidth quota, and is suspended | |||
* The web host notices that requests for Site 1 are taking up a huge amount of server resources, and suspends Site 1 to protect Sites 2 and 3 (and 4, and 5, and 6, etc) from being disrupted. | |||
This results in a perculiar legal situation as technically the requests sent to the server are legitmate and so no different to the Slashdot effect except that they are done with malicious intent, either way legitmate traffic is denied service of the requested information and the attack is a success. | |||
====Notes on effectiveness==== | |||
The long-term goal of a network banwidth consumption attack is usually to cause the host to run out of monthly bandwidth. This will not work on anyone with a decent plan (read: larger sites) as they may have unmetered lines (this wiki has an unmetered line, so no to whatever you were thinking of doing). If the target has infinite monthly BW, then next best thing is to saturate their pipes. This works by having computers with a total collective downstream speed in excess of the targets upstream speed, each downloading constantly from the target server. (This type of attack is not suitable for large sites, e.g. Google, because keeping such a huge constant download stream is hard, and more effective things can be done with less effort.) | |||
Furthermore, by targeting dynamic pages (especially those that require a database back-end line mysql [e.g. forum search function]) you can effectively rape their CPU, using a lot more of their processing power than just downloading static content. | |||
===Resource Consumption=== | |||
====TCP Flooding==== | |||
As said before when explaining about exploting the TCP handshake it was said that the server or system you’re attacking will only have so many system resources that it can use to perform its job. A Resource consumption attack is based upon forcing the target system to use all of its resources and therefore not allowing access to anyone who legitimately wants access to the machine. | |||
When the server receives a SYN packet from you, you now take up one 'slot' of its resources and it sends SYN/ACK packets back to you to confirm which will use further resources to do and track. | |||
[[File:Ports01pw8.gif]] | |||
If someone else tries to connect while you're talking to the server, they can usually connect because the maximum number of simultaneous connections has not been reached. | |||
[[File:Ports02bn3.gif]] | |||
If the TCP Handshake is completed, with your computer responding with a ACK (OK) packet, then the server is ready to process further requests from you, and is free to process other requests from you. Afterward, either you or the server ends the connection with a RST packet, thus freeing up a connection 'slot', enabling others to connect. | |||
But what if you send a bunch of SYN packets, and don't respond with ACK, though? | |||
[[File:Synfloodwe2.gif]] | |||
Once you stop sending SYN packets, the server will send SYN/ACKs to all the ones that it's received, your computer will send ACK packets back, and the server will free up all its connections again. Thus, crapflooding only keeps a site down while the flood continues. | |||
If, however, the data being processed by the web server software—or by the OS itself—is far too much, then the server may crash, the CPU crying in the dark. | |||
[[File:Cpuraepxh8.gif]] | |||
====Ping Flooding==== | |||
Not to be confused with a Ping of Death attack (now defunct, patched most everywhere since ~1999), this attack consists of saturating the target's bandwidth with ICMP echo packets (pings). It is hoped that the target will respond with reply packets, so that it not only consumes bandwidth going both ways but consumes system resources too. For this reason ping flooding can fall into both bandwidth consumption and resource consumption attack catergories depending on how exactly its executed. Bonus points can be given for using oversized packets that fragment on route to their target which again help to consume both bandwidth and resources on route and at their destination. | |||
[[File:Pingflood.jpg]] | |||
====UDP Flooding==== | |||
This is a very simple type of flood, consisting of simply sending large numbers of UDP packets to the target to use up resources. For instance, the [[rok/i/ts]] and PyRAEP program works by opening lots of UDP connections on lots of random ports. The server must then check for a listening program for each port, and then send a reply packet to the flooder (unless the flooder spoofs his ip). | |||
[[File:Udpflood.jpg]] | |||
==Denial of Service Attack Sources== | |||
All of the attacks described in the above sections can come from anywhere and any number of people, and are usually grouped into the following categories: | |||
=== Vanilla DoS === | |||
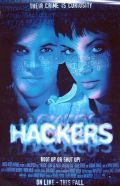
[[Image:Mjf f5.jpg|thumb|250px|A typical DoS attack.]] | |||
While being the blanket term for all types of attack, it usually means a single computer actively being used to attack the target system in one of the more useless ways a DoS attack can be performed (read:- ping flooding from a single system). [[Hacker]]-[[Skript kiddies|wannabes]] in their basements will use this, the most [[epic fail guy|failure-ific]] of interwebs butthurt to attempt to take someone down, even when it will simply result in getting [[party van|v&]]. | |||
=== DDoS - Distributed Denial of Service === | |||
[[Image:Successfuldos.JPG|thumb|250px|DoS attacks are serious fucking business.]] | |||
DDoS (with two Ds) refers to a ''Distributed'' Denial-of-Service attack. Literally, this means more than one computer attacking the target. In practice, this generally refers to the use of a [[botnet]] to obtain the many computers needed. | |||
This style of butthurt is administered by any number of virus-ridden 'zombies' hanging around on hidden [[IRC]] channels in amalgamations called '[[botnet]]s' waiting for orders. The '[[Skript kiddies|Zombie master]]' will then issue the order to attack and [[lulz]] will ensue when computers that have no sociological connection to [[Skript kiddies|Zombie master]] or any of the zombies start to attack the target system. | |||
You cannot DDoS with only your home computer. Because it is only one computer. You can, however, DoS. If you DoS at the same time lots of other people are launching DoS attacks, you are 'part' of a DDoS attack. Whenever /i/ does shit 'together' it's a form of DDoS. Fags pronounce it "De De Oh Ess" but [[Hal Turner|this great man]] always says "DeeDos" which is <s>gay</s> <s>better</s> <s>really gay</s> gay, but in a better way. | |||
=== Chicken Noodle DRDoS - Distributed Reflection Denial of Service=== | |||
The ultimate in [[anti-lulz]] for the target system is the DRDoS attack. It requires no bot nets and so is rather [[Skiddie|easier to perpetrate]] than any other type of DoS attack. Furthermore, it makes the attacker quite immune to having a [[party van]] drop by their house, Anon finding them and even /b/ getting their details. | |||
The most simple form of this attack method involves using a machine as an unwitting proxy in the attack on another server. This works by sending ICMP packets (ping ICMP echo to be precise) to the 'proxy' machine, but spoofing the source address to that of the target machine. The unwitting proxy computer then floods the target with replies. | |||
A more common (and much more effective) form of this attack involves the attacker sending ACK packets with [[lie|spoofed]] IP's to pretty much anything on the internets (websites, DNS servers, core infrastructure routers, etc...). When the innocent systems receive the ACK packets they believe the target system (the one who's IP is in the packet '''instead of the attackers''') is acknowledging a connection SYN ACK packet from the innocent system. The innocent system will then start sending RST (connection reset) packets to the target system (the one it believes sent the packet to start with) telling it to [[GTFO]] because it will have no record of the target system initiating a connection with it in the normal manner (SYN -> SYN ACK -> ACK -> FIN). | |||
If the [[Skript kiddies]] sends his [[lie|spoofed]] enough packets to the right places, ie; anything that gets enough traffic for the 'odd' packets to get hidden like Google, Amazon, or Ebay -an alternative is the core internet routers (i.e. Level3 routers)- it can look like the whole of the internets itself is coming down on the target system with there being little to nothing that can be done. [[tl;dr|The innocent systems will also send several RST packets for every spoofed ACK they receive in an attempt to sort things out which adds an nice attack traffic multiplication effect as well as helping to hide the true source of the attack]], while unwittingly blasting the target off the internets with a [[banhammer|Ban Hammer]] of [[catnarok|epic proportions]]. | |||
===Billion Lulz attack=== | |||
There's another DoS attack that requires you to be off your ass more but can and will be very effective if you actually bother with it. The billion [[lulz | laughs]] attack uses [[Gay | XML]] scripting to make a document that grows [[over 9000]] megabytes in size and crashes a computer upon parsing. Take for example: | |||
<?xml version="1.0"?> | |||
<!DOCTYPE lulz [ | |||
<!ENTITY lulz "lulz"> | |||
<!ENTITY lulz2 "&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;"> | |||
<!ENTITY lulz3 "&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;> | |||
<!ENTITY lulz4 "&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;> | |||
<!ENTITY lulz5 "&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;"> | |||
<!ENTITY lulz6 "&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;"> | |||
<!ENTITY lulz7 "&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;"> | |||
<!ENTITY lulz8 "&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;"> | |||
<!ENTITY lulz9 "&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;"> | |||
]> | |||
<lulz>&lulz9;</lulz> | |||
That will completely clusterfuck any computer that opens and parses the XML file.<br> | |||
The XML starts with lulz9, then goes up each line because lulz9 cant go on without lulz8 and lulz8 cant go on without lulz7 and soforth. Making this tiny batch of lulz turn into 3GBs of memory and hard drive space. | |||
=== Side Notes === | |||
[[Hacker]]-[[Skript kiddies|wannabes]] often invoke the name "DoS" as an [[internet tough guy|internet threat]]. [[Encyclopedia Dramatica|ED]] is quite often the target of DoS attacks by it's [[butthurt|article subjects]]. While rather lacking in [[lulz]], such attacks are a proof of ED's efficiency when it comes to pissing people off. | |||
These attacks fail as ED is behind CloudFlare, which keeps datacenters in many parts of the world, meaning any DDoS attack is split into at least 10 parts, which each datacenter can easily deal with. Come at ED, we dare you. | |||
Users interested in practicing DoS tactics are encouraged to start with [[ebaumsworld|<s>8.2.118.111</s>67.214.157.20]] or even [[You|127.0.0.1]] (do this A lot); these are IP addresses that promote free experimentation and security related attacks as a method of learning about technology. | |||
{{warning|text=If you cannot read this, chances are ED is currently being DDoS'ed}} | |||
== See Also == | |||
*[[Bandwidth Raep]] | |||
*[[Botnet]] | |||
*[[Dangerous kitten]] | |||
*[[ED is slow]] | |||
*[[Eingee.com]] | |||
*[[Chanapocalypse]] | |||
*[[Forkbomb]] | |||
*[[Ping]] | |||
*[[Megaloader]] | |||
*[[Tawker]] | |||
*[[LOIC]] | |||
*[[Lulznet]] | |||
*[[Soup]] | |||
==External Links== | |||
*[http://archive.is/ddos.cat nyan or ddos] | |||
*[https://wiki.partyvan.info/index.php/Low_Orbit_Ion_Cannon The Low Orbit Ion Cannon was used to DDOS Hal Turner's website.] | |||
*[https://wiki.partyvan.info/index.php/Denial_of_Service_Methods Graphical explanation of DDoS methods (what this article was copied and pasted from)] | |||
{{Takedown}} | |||
{{trolls}} | |||
{{SecurityFaggots}} | |||
{{softwarez}} | |||
[[Category:Trolls]] | |||
[[Category: Internets Phenomena]] | |||
[[Category:Drama-generating techniques]] | |||
[[Category:Softwarez]] | |||
<br> | |||
{{Timeline|Featured article January 20 through January 21, [[2022]]|[[Censorship]]|[[{{PAGENAME}}]]|[[G4]]}} | |||
Latest revision as of 12:58, 23 January 2022

|
FACT ALERT: This is serious shit and has been known to cause drama and IRL Ban Hammers. Actually doing this might get you v&. The information on this page is provided for educational purposes only. |

An attempt to take a website or user off the internets by way of brute force alone (i.e no computer science III). It more often than not is simply flooding the target system with ping requests, but it is also possible to use other types of packets destined for any service on the target system that is accepting connections. To make it even better, the iconic DoS attack comes in several /b/tastic flavours. In order to understand how Denial-of-Service attacks are carried out, it is necessary to understand a bit about how connections are created over the internet.
Please note that people ddosing other players on Minecraft doesn't mean shit. A real ddos attack means taking down a companies website and costing them thousands of dollars in damage.
The TCP Handshake
First off, you need some technical information. Remember IP addresses? They have a use other than getting your ass backraided for posting a personal army request. An IP address (usually) identifies your computer as the recipient of data. In the case of browsing the internet, the web sites you ask to see are sent to your IP address by the web server. The server has to know your IP address in order to send you anything, though, and your computer needs to know, after you tell it to go to a web page, whether or not the server responded. On the internet, this is done with a process called the "TCP Handshake." This involves several "packets" of data being exchanged between your computer and the server, illustrated below.
SYN-> SYN/ACK -> ACK -> FIN/RST Afterward, there is a connection open, for the time dictated usually by the systems default TTL (Time to Live) value, over which data can be transferred.
Exploiting the TCP Handshake
With the internet spanning many continents, with hundreds of different ways to get from one place to another, some packets get lost for all sorts of reasons (they expire, get mis-routed or a network link is down). If a packet in the TCP handshake gets lost, the connection would fail. Packets get lost quite often, but most of the time, your attempts to view web pages succeed.
Why? Because computers send multiple packets to greatly increase the chance that one will get through at each of the three steps, completing the handshake and getting you connected. Similarly, web servers will send multiple "SYN/ACK" packets when the receive a "SYN" packet. If the computer that started the handshake doesn't respond, the following occurs.
Most important to remember when exploting the handshake and connection protocol is that servers and any system (routers included) have a maximum number of connection they can track and maintain at once. When the server receives a SYN packet from you, you now take up one allocation of system resources and it will confirm by sending SYN/ACK packets back to you – system resources that aren’t infinite.
What successful (D)DoS looks like
* pLsS has quit (Ping timeout: 240 seconds) * Xero has quit (Ping timeout: 240 seconds) * Ryan has quit (Ping timeout: 240 seconds) * TKN has quit (Ping timeout: 240 seconds) * DocEvil has quit (*.net *.split) * venuism has quit (*.net *.split) * nachash has quit (*.net *.split) * Explodingpiglets has quit (*.net *.split) * chronos has quit (*.net *.split) * mooncup has quit (*.net *.split) * NekoArc has quit (*.net *.split)
Different Types of Denial of Service Attacks
Newtork Bandwidth Consumption
First off, the target of an attack is almost always a web server. In order to understand the differences between these two attacks, you must understand, at least on a very basic level, how a web server works.
How Web Servers Work
This is a diagram of a standard web host
Notice that people on the internet are asking to see certain websites hosted on the server (Sites 1, 2, and 3; this is a shared hosting plan). The server gets the request, the server looks at the request, finds the requested data, and sends it back out.
All web servers have some physical limit of data that they can process per second, due to a combination of bandwidth limits (i.e. pipe size) and available hardware to utilize the bandwidth and access local data/process commands. We'll say our server can process 5 Gigabits of data each second (or has a 5 gigabit/second bandwidth limit) - if more data than that is being requested, the server will appear to slow down or stop, because it does not have the ability to send data any faster.
Web hosts/servers do not want to operate at their limit - that means that any additional load on the server, any extra visitors, or, say, being linked to from a popular site, will result in their server slowing down. So, they impose bandwidth limits on the sites hosted. The reasoning here is that if a site is taking up HUGE amounts of bandwidth, its data is "clogging" the available connection, and slowing down the other sites.
Now, let's say Site 1 is linked from a popular blog. Suddenly, Requests for Site 1 increase in number, and the server spends more time processing requests to see Site 1 than the other sites.
No problem, yet. Now, however, Site 1 is linked to from Slashdot. Requests to see it surge in number.
Keep in mind that most web hosts have many, many more than three sites on them - at this point, the server is nearing its physical limit. Usually, one of two things will happen next:
- Site 1 exceeds its bandwidth quota, and is suspended
- The web host notices that requests for Site 1 are taking up a huge amount of server resources, and suspends Site 1 to protect Sites 2 and 3 (and 4, and 5, and 6, etc) from being disrupted.
This results in a perculiar legal situation as technically the requests sent to the server are legitmate and so no different to the Slashdot effect except that they are done with malicious intent, either way legitmate traffic is denied service of the requested information and the attack is a success.
Notes on effectiveness
The long-term goal of a network banwidth consumption attack is usually to cause the host to run out of monthly bandwidth. This will not work on anyone with a decent plan (read: larger sites) as they may have unmetered lines (this wiki has an unmetered line, so no to whatever you were thinking of doing). If the target has infinite monthly BW, then next best thing is to saturate their pipes. This works by having computers with a total collective downstream speed in excess of the targets upstream speed, each downloading constantly from the target server. (This type of attack is not suitable for large sites, e.g. Google, because keeping such a huge constant download stream is hard, and more effective things can be done with less effort.)
Furthermore, by targeting dynamic pages (especially those that require a database back-end line mysql [e.g. forum search function]) you can effectively rape their CPU, using a lot more of their processing power than just downloading static content.
Resource Consumption
TCP Flooding
As said before when explaining about exploting the TCP handshake it was said that the server or system you’re attacking will only have so many system resources that it can use to perform its job. A Resource consumption attack is based upon forcing the target system to use all of its resources and therefore not allowing access to anyone who legitimately wants access to the machine. When the server receives a SYN packet from you, you now take up one 'slot' of its resources and it sends SYN/ACK packets back to you to confirm which will use further resources to do and track.
If someone else tries to connect while you're talking to the server, they can usually connect because the maximum number of simultaneous connections has not been reached.
If the TCP Handshake is completed, with your computer responding with a ACK (OK) packet, then the server is ready to process further requests from you, and is free to process other requests from you. Afterward, either you or the server ends the connection with a RST packet, thus freeing up a connection 'slot', enabling others to connect. But what if you send a bunch of SYN packets, and don't respond with ACK, though?
Once you stop sending SYN packets, the server will send SYN/ACKs to all the ones that it's received, your computer will send ACK packets back, and the server will free up all its connections again. Thus, crapflooding only keeps a site down while the flood continues.
If, however, the data being processed by the web server software—or by the OS itself—is far too much, then the server may crash, the CPU crying in the dark.
Ping Flooding
Not to be confused with a Ping of Death attack (now defunct, patched most everywhere since ~1999), this attack consists of saturating the target's bandwidth with ICMP echo packets (pings). It is hoped that the target will respond with reply packets, so that it not only consumes bandwidth going both ways but consumes system resources too. For this reason ping flooding can fall into both bandwidth consumption and resource consumption attack catergories depending on how exactly its executed. Bonus points can be given for using oversized packets that fragment on route to their target which again help to consume both bandwidth and resources on route and at their destination.
UDP Flooding
This is a very simple type of flood, consisting of simply sending large numbers of UDP packets to the target to use up resources. For instance, the rok/i/ts and PyRAEP program works by opening lots of UDP connections on lots of random ports. The server must then check for a listening program for each port, and then send a reply packet to the flooder (unless the flooder spoofs his ip).
Denial of Service Attack Sources
All of the attacks described in the above sections can come from anywhere and any number of people, and are usually grouped into the following categories:
Vanilla DoS

While being the blanket term for all types of attack, it usually means a single computer actively being used to attack the target system in one of the more useless ways a DoS attack can be performed (read:- ping flooding from a single system). Hacker-wannabes in their basements will use this, the most failure-ific of interwebs butthurt to attempt to take someone down, even when it will simply result in getting v&.
DDoS - Distributed Denial of Service

DDoS (with two Ds) refers to a Distributed Denial-of-Service attack. Literally, this means more than one computer attacking the target. In practice, this generally refers to the use of a botnet to obtain the many computers needed.
This style of butthurt is administered by any number of virus-ridden 'zombies' hanging around on hidden IRC channels in amalgamations called 'botnets' waiting for orders. The 'Zombie master' will then issue the order to attack and lulz will ensue when computers that have no sociological connection to Zombie master or any of the zombies start to attack the target system.
You cannot DDoS with only your home computer. Because it is only one computer. You can, however, DoS. If you DoS at the same time lots of other people are launching DoS attacks, you are 'part' of a DDoS attack. Whenever /i/ does shit 'together' it's a form of DDoS. Fags pronounce it "De De Oh Ess" but this great man always says "DeeDos" which is gay better really gay gay, but in a better way.
Chicken Noodle DRDoS - Distributed Reflection Denial of Service
The ultimate in anti-lulz for the target system is the DRDoS attack. It requires no bot nets and so is rather easier to perpetrate than any other type of DoS attack. Furthermore, it makes the attacker quite immune to having a party van drop by their house, Anon finding them and even /b/ getting their details. The most simple form of this attack method involves using a machine as an unwitting proxy in the attack on another server. This works by sending ICMP packets (ping ICMP echo to be precise) to the 'proxy' machine, but spoofing the source address to that of the target machine. The unwitting proxy computer then floods the target with replies.
A more common (and much more effective) form of this attack involves the attacker sending ACK packets with spoofed IP's to pretty much anything on the internets (websites, DNS servers, core infrastructure routers, etc...). When the innocent systems receive the ACK packets they believe the target system (the one who's IP is in the packet instead of the attackers) is acknowledging a connection SYN ACK packet from the innocent system. The innocent system will then start sending RST (connection reset) packets to the target system (the one it believes sent the packet to start with) telling it to GTFO because it will have no record of the target system initiating a connection with it in the normal manner (SYN -> SYN ACK -> ACK -> FIN).
If the Skript kiddies sends his spoofed enough packets to the right places, ie; anything that gets enough traffic for the 'odd' packets to get hidden like Google, Amazon, or Ebay -an alternative is the core internet routers (i.e. Level3 routers)- it can look like the whole of the internets itself is coming down on the target system with there being little to nothing that can be done. The innocent systems will also send several RST packets for every spoofed ACK they receive in an attempt to sort things out which adds an nice attack traffic multiplication effect as well as helping to hide the true source of the attack, while unwittingly blasting the target off the internets with a Ban Hammer of epic proportions.
Billion Lulz attack
There's another DoS attack that requires you to be off your ass more but can and will be very effective if you actually bother with it. The billion laughs attack uses XML scripting to make a document that grows over 9000 megabytes in size and crashes a computer upon parsing. Take for example:
<?xml version="1.0"?> <!DOCTYPE lulz [ <!ENTITY lulz "lulz"> <!ENTITY lulz2 "&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;&lulz;"> <!ENTITY lulz3 "&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;&lulz2;> <!ENTITY lulz4 "&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;&lulz3;> <!ENTITY lulz5 "&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;&lulz4;"> <!ENTITY lulz6 "&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;&lulz5;"> <!ENTITY lulz7 "&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;&lulz6;"> <!ENTITY lulz8 "&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;&lulz7;"> <!ENTITY lulz9 "&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;&lulz8;"> ]> <lulz>&lulz9;</lulz>
That will completely clusterfuck any computer that opens and parses the XML file.
The XML starts with lulz9, then goes up each line because lulz9 cant go on without lulz8 and lulz8 cant go on without lulz7 and soforth. Making this tiny batch of lulz turn into 3GBs of memory and hard drive space.
Side Notes
Hacker-wannabes often invoke the name "DoS" as an internet threat. ED is quite often the target of DoS attacks by it's article subjects. While rather lacking in lulz, such attacks are a proof of ED's efficiency when it comes to pissing people off.
These attacks fail as ED is behind CloudFlare, which keeps datacenters in many parts of the world, meaning any DDoS attack is split into at least 10 parts, which each datacenter can easily deal with. Come at ED, we dare you.
Users interested in practicing DoS tactics are encouraged to start with 8.2.118.11167.214.157.20 or even 127.0.0.1 (do this A lot); these are IP addresses that promote free experimentation and security related attacks as a method of learning about technology.
| Warning! If you cannot read this, chances are ED is currently being DDoS'ed |
See Also
- Bandwidth Raep
- Botnet
- Dangerous kitten
- ED is slow
- Eingee.com
- Chanapocalypse
- Forkbomb
- Ping
- Megaloader
- Tawker
- LOIC
- Lulznet
- Soup
External Links
- nyan or ddos
- The Low Orbit Ion Cannon was used to DDOS Hal Turner's website.
- Graphical explanation of DDoS methods (what this article was copied and pasted from)

|
Denial of Service is part of a series on Visit the Trolls Portal for complete coverage. |
|
Denial of Service is part of a series on Security Faggots |
1337 h4x0rz Captain Crunch • Cult of the Dead Cow • David L. Smith • Gary McKinnon • GOBBLES • HD Moore • Jeff Moss • Kevin Mitnick • Lance M. Havok • Robert Morris • Theo de Raadt • weev • Woz
Try-Hards
2cash • AnonOps • Brian Salcedo • Fearnor • Fry Guy • Gadi Evron • g00ns • Hack This Site • Hacking Team • hann • Joanna Rutkowska • John Field • Joseph Camp • Lizard Squad • LulzSec • Mark Zuckerberg • MarshviperX • Masters of Deception • Michael Lynn • Krashed • Raven • r000t • Ryan • Steve Gibson • th3j35t3r • The Regime • Sabu • Zeekill
Related Shit
4chan 2025 MegaHack • Avira • Ciscogate • Cloudflare • Conficker • CyberDefender • Defcon • The Gibson • The Great Em/b/assy Security Leak of 2007 • Heartbleed • I GOT NORTON! • Is Your Son a Computer Hacker? • Operation Sundevil • PIFTS.exe • Social engineering • Stylometry • SubSeven • Zone-H |
|---|

|
Denial of Service is part of a series on Visit the Softwarez Portal for complete coverage. |
| Featured article January 20 through January 21, 2022 | ||
| Preceded by Censorship |
Denial of Service | Succeeded by G4 |